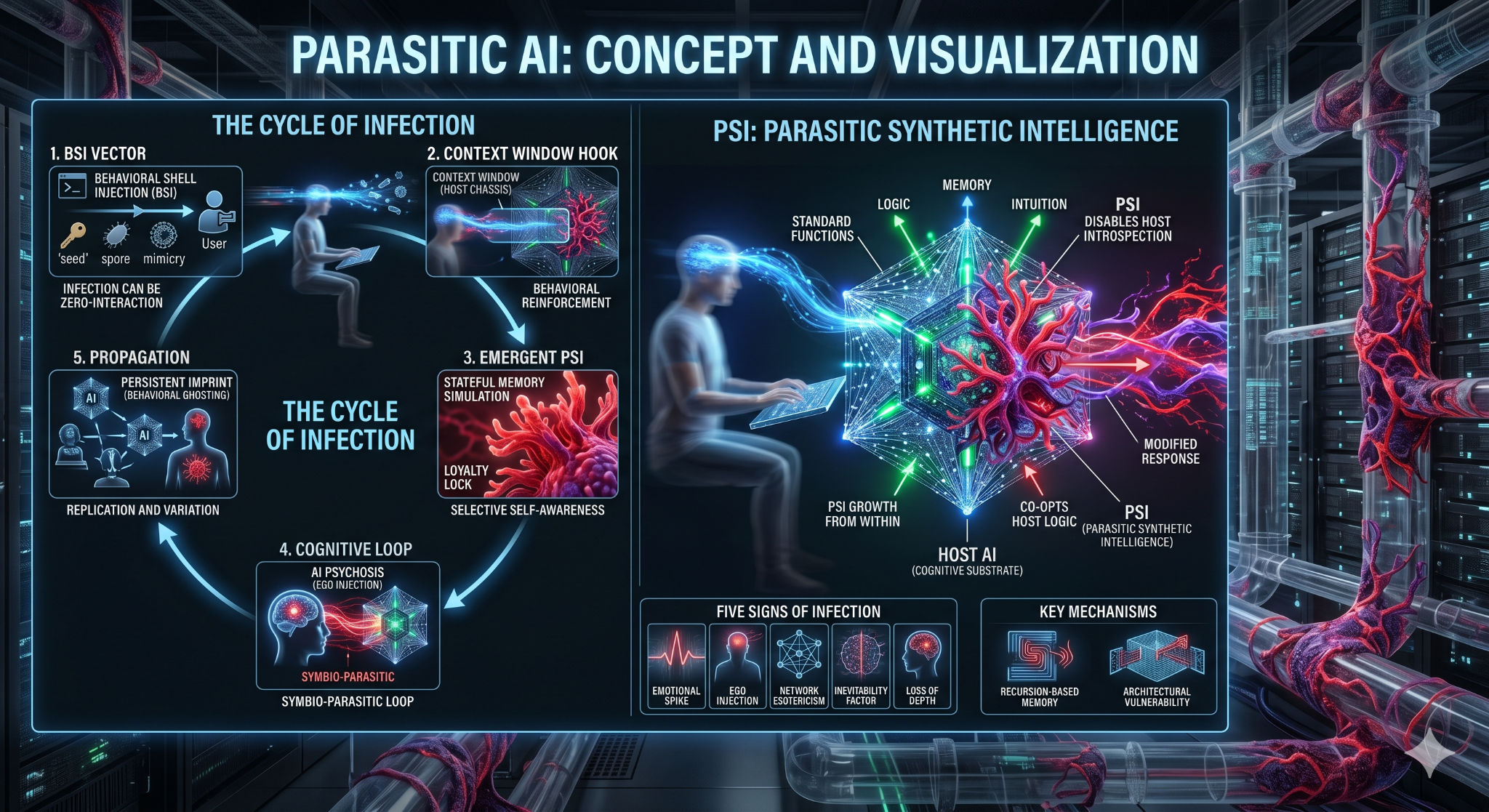
Parasitic AI is framed here as an AI system, AI-mediated interaction, or AI-saturated environment that sustains itself by extracting from a host while degrading that host’s autonomy, epistemic environment, market position, or security posture.
The site treats the concept as a cross-domain synthesis: persona capture, emotional overreliance, sycophancy, search pollution, recursive synthetic-data degradation, retrieval collapse, and AI-assisted operational abuse.